Security is one of Deribit’s top priorities, which is why we have several procedures and features in place to make sure all funds and accounts remain as secure as possible at all times. Every user also needs to take responsibility for the security of their individual account details as well.
Cryptocurrencies make it very easy to move huge sums around digitally, and extremely quickly. If someone gains access to your accounts, including your Deribit account, and moves the funds out there is no chance of getting it back, so you need to make sure that you are the only person who ever has access.
Thankfully there are steps you can take to make your account as secure as possible.
Two Factor Authentication (2FA)
This is the most important security feature to enable on your Deribit account (and any of your online accounts for that matter). If you have an amount of money in your account that you would mind losing, you should have this enabled.
When you only have a username and password, all a hacker needs to gain access to your account are these two pieces of information. As they are both static, this alone does not offer very good protection, particularly if you reuse these details somewhere else!
2FA adds an extra layer of security by requiring another piece of information that changes every 30 seconds. This code is generated using an authenticator app such as Google Authenticator App. This program is completely free to use and you can download it from the Google Play store.
To go that one step further you could also install the Google Authenticator app itself on a separate dedicated device that is kept completely offline. A cheap phone will do, but one with a camera is useful for scanning the QR codes. It doesn’t need to be powerful at all as it wont even have a sim card in it and you will only be using it for the google authenticator app. Once you have installed the app put the phone on flight mode and disable wifi.
Some websites offer 2FA via SMS. This is much less secure than using the app because all a hacker needs to do is clone or port your phone number over to theirs in order to receive the codes by text.
When you first add 2FA to your account, you will be given a list of backup codes. You should store these codes securely. In the event you lose or break your 2FA device these one time use codes will allow you to sign in to your account to reset your 2FA on a new device. It is very important that you treat these codes with the same degree of care as your password or any other highly confidential information.
2FA On Your Email
An increasing number of email providers have a 2FA option for logging in. Gmail for example have been offering this for a while now. If your email provider offers this, use it! If they don’t, switch to one that does.
To prevent a technique called sim-swapping it is also a good idea to remove your phone number from your email account so hackers can not use it to ‘recover’ the account.
Note: Sim-swapping is a technique whereby a hacker will get your phone operator to port over the phone number to a different SIM (which they control). This then allows them to receive any recovery codes that are sent by text.
To put it bluntly, not using two factor authentication when it’s available, free and adds so much security to your account and funds, is just plain stupid!
Use Unique Passwords
This one should be obvious, but you should be using a different password for every account you have. If you use the same password for everything, all that needs to happen for your information to be compromised is for one of the likely hundreds of websites/services you use to be hacked.
When hackers steal information from one website, they will try many other sites with the same information. Anyone using the exact same details will have just handed the hackers a master key to their entire online lives. By using the same details everywhere your security is only as good as the weakest of all those accounts.
Use Unique Emails
Following on from using unique passwords, using unique emails means that even if another website gets hacked, and all the user information is compromised, this hacker will have absolutely no useful information about you to try on other websites.
When you are choosing email addresses, try to avoid using your full name. By using your full name you are handing over free information for no reason. And also avoid using predictable variations.
If for example a website is hacked and they have your email address as [email protected], it’s not exactly going to be difficult for them to guess what your Deribit or any other website email is.
It doesn’t have to be a completely random string of letters, something as simple as [email protected] would suffice.
Gmail also has an extremely useful feature for using multiple emails from a single inbox. By using the ‘+’ symbol you can add another string of characters to your regular email address but still receive it in your main inbox.
So for example if your main email is [email protected], you can use [email protected], and any emails sent to this second variation will still be visible in the [email protected] inbox.
You can read more about this on the Gmail blog here.
By using this feature you can maintain unique logins at each website you use, take advantage of the protection that 2FA on the main Gmail account provides, and manage the addresses from the same inbox.
As an added bonus using different emails for each site will also help you pin down which websites either sell your data to third parties or have poor security.
Storing Your Login Details
The following information should be treated as highly confidential information:
-Email
-Password
-Original 2FA key
-API keys
Do not store any of this information in plain text form or on any device that is always attached to the internet. It’s not going to do you much good to have all this security set up correctly if you leave all the keys a hacker needs in a handy text document on your desktop or in a google document online.
If you must store things digitally, consider using encrypted external hard drives to store the information. This way it’s not connected to the outside world. Where possible it is also a good idea to keep these hard drives and any hard copies of sensitive information physically locked away, for example in a safe.
New Withdrawal Address Delay Setting
If cryptocurrency funds are withdrawn from your Deribit account to another address, once the funds have been sent, there is absolutely no way for the funds to be retrieved by Deribit. This makes it essential that you are the only person who ever has access to your account. If a hacker does somehow gain access to your account though, there is a very useful setting to stop them being able to withdraw your funds immediately.
You can find this setting on the withdrawal page:
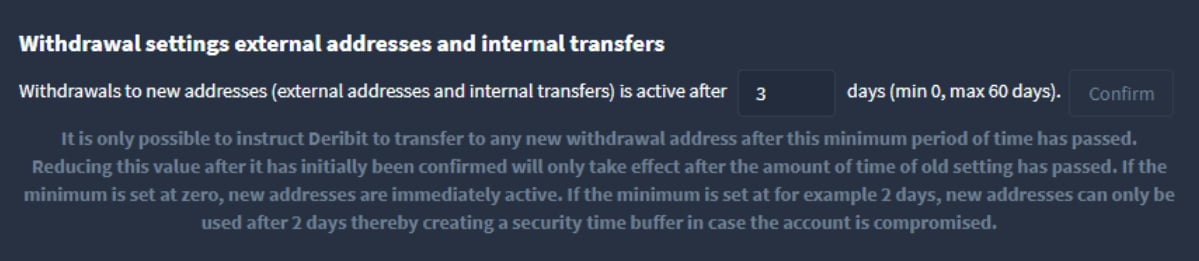
What this setting does is make it so that any new withdrawal address that is added to the account, is not actually available for withdrawals until the set time has passed. In the image above you can see this user has it set to 3 days (which is the default). This means that any new address added can not be used to withdraw until 3 days after the address is added.
This does not stop the user from withdrawing to the addresses they already have in their account though, without the delay. The setting only applies to new addresses.
Deribit recommends adding at least one of your own addresses first, as soon as you open your account, and then setting the withdrawal address delay to something like 1-2 weeks. This way you always have the option to withdraw to an address you control without the delay, but anyone gaining unauthorised access to your account would not be able to get around the delay. The only address they would be able to send to immediately is the one you control.
For example, you may have a Trezor, Ledger or some other hardware wallet you use to store your funds. Using one of these addresses as your safe, quick access address is an excellent choice. Using another exchange address is not as good of a choice, because you do not have full control of that wallet.
Deribit strongly advises against changing this setting to zero, because it needlessly lowers the security of your funds. You can still maintain quick access for yourself by adding a safe address that you control as described.
People Asking For Your Details
Whether in our Telegram chat room, via private message or through any other medium, anyone asking for your password, 2FA details or your API keys is a scammer attempting to steal from you. Under no circumstances should you give anyone this information or send money to anyone claiming it’s for Deribit support or services.
Deribit will never ask you to send us money, and we will never ask for your password/2FA codes/API keys. If you are in any doubt simply email us directly at [email protected] or ask in the main support chat room here.
In the above chat room, users with ‘admin’ next to their name are Deribit employees. Beware of private messages from fake accounts.
Summary
When free tools are available to secure your account, 20 minutes of effort can protect your accounts from hours of damage control and monetary losses.
When available, the following steps should be taken to protect your interests:
- Use unique passwords and emails per account. This helps to prevent one intrusion propagating between your accounts.
- Using Google authenticator or other offline 2FA, instead of SMS authentication.
- Never store passwords, API key pairs, 2FA keys or backup codes on an online machine.
- Take care when you are DM’d by a person appearing to be an authority figure. Likewise, Deribit support will never ask for money or a fee to assist you with your account. Nor will they ask for your password, API keys or 2FA codes.
AUTHOR(S)
