Image explanation: A turkey using “evidence”; unaware of Thanksgiving, it is making “rigorous” future projections based on the past. Credit: George Nasr
Today we regale the reader with a story of how a particular crowd-sale smart contract was exploited by a founding team member a year after its launch. This may change the way you think about trust-minimization and hidden vulnerabilities in the smart contract space more broadly.
Humble beginnings
Oyster Pearl (PRL) was a project born during the ICO boom of 2017. It claimed to combine concepts from the Ethereum and IOTA blockchains to provide decentralized and anonymous file storage. The PRL token sale began in late October 2017 and ended relatively quietly 3 weeks later with only 300 ETH raised (~$90,000 at the time) in exchange for 1.5 million PRL, a rate of 5000 PRL: 1 ETH. On December 17th, with the general euphoria surrounding cryptocurrency starting to grow, the Oyster team decided to place 25 million PRLs in 5 separate sell walls on EtherDelta ranging from 5 to 9 cents. They raised roughly $1.75 million over the next few days and the project had a market capitalization of over $2 million. By this time, 47.1% of the total token supply had been sold to the public.
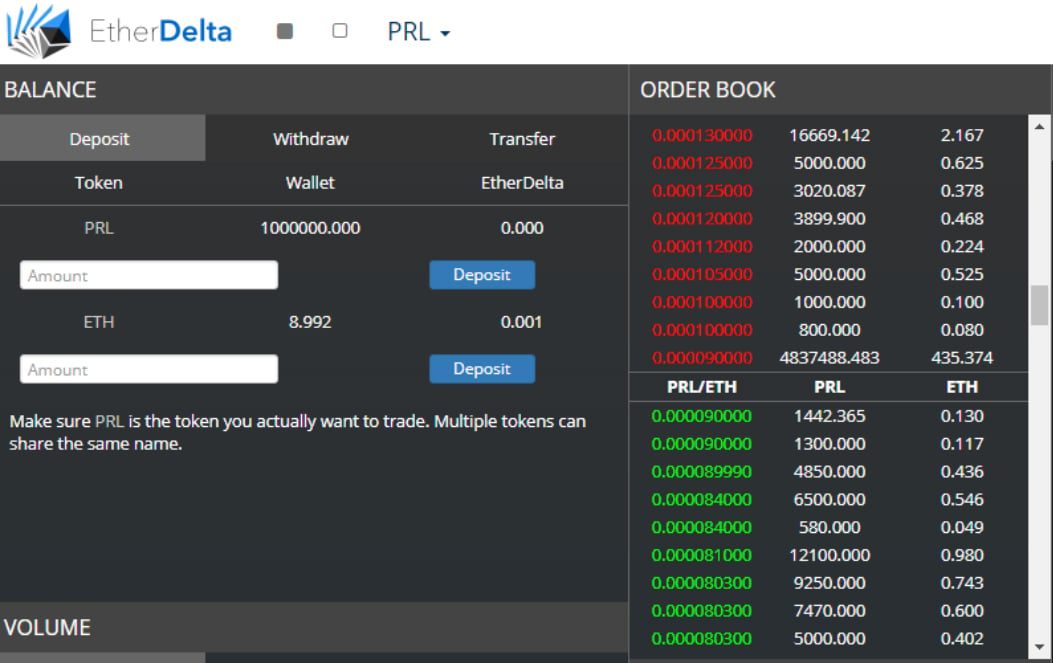
PRL EtherDelta Coin Offering.
Source: Oyster Pearl ETHERDELTA Coin Offering almost finished
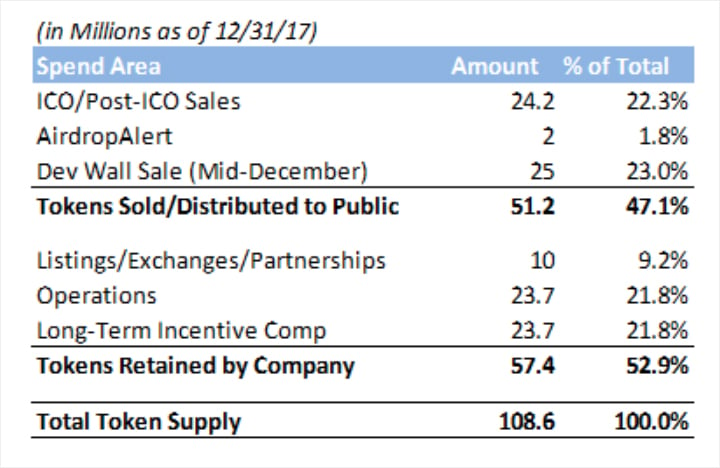
PRL Token Distribution. Source: Oyster Pearl Team Update – William Cordes
Oyster Pearl achieved a market cap of over $240 million in January 2018, at the height of the ICO bubble. The price per PRL was over $4, meaning a 66x versus the seed price and a 40-80x versus the EtherDelta sell wall, and volume was frenetic on KuCoin–a major altcoin exchange. This same market cap today would make it a top 30 coin, in line with the market cap of ZCash.
Afterward, PRL crashed dramatically with the rest of the ICO market but there was otherwise nothing unusual about it compared to other ICOs at the time. While some projects were brazenly exit scamming and disappearing, Oyster Pearl appeared to be building. They shipped code on Github and eventually delivered mainnet in May. One notable development was a major leadership change: the then-anonymous CEO and founder, Bruno Block, transferred leadership to Bill Cordes, previously the CFO, on June 9th.
From September 28th to October 29th, PRL rose from 6 cents to a peak of 23 cents. Its price versus BTC neared the highs of Q1 2018, allegedly on rumors of an impending Binance listing.

Source: Coinmarketcap.com
Insider attack
In the early hours of October 30th, disaster struck as millions of PRL were suddenly liquidated on KuCoin without any warning.
Bill Cordes frantically asked KuCoin to shut down all PRL markets, but by the time they were shut, an estimated $300,000 worth of proceeds in BTC and ETH had already been withdrawn.

PRLBTC Price Chart on KuCoin. Source: Link
The Oyster Pearl smart contract had been exploited via a trapdoor mechanism which had existed since inception. This allowed Bruno Block to make a “transferDirector()” call from another address to reopen the ICO contract to mint more PRL and transfer any ETH used back out of the contract.
1. The Oyster smart contract allowed the contract private key owner to re-open the crowdsale at any point:
/**
* Director can open the crowdsale
*/
function openSale() public onlyDirector returns (bool success) {
// The sale must be currently closed
require(saleClosed);
// Unlock the crowdsale
saleClosed = false;
return true;
}
2. Block #6605271 – the openSale() was invoked: Link
3. Block #6605281 – 50 ETH was sent to the smart contract from
0x0001ee57bb28415742248d946d35c7f87cfd5a54 and creates 250,000 PRL: Link
4. ETH continued to be sent in the following blocks to create new PRL:
- 6605299 | 50 ETH – 250,000 PRL
- 6605340 | 50 ETH – 250,000 PRL
- 6605366 | 50 ETH – 250,000 PRL
- 6605608 | 73 ETH – 356,000 PRL
- 6606268 | 186 ETH – 930,000 PRL
- 6606409 | 175 ETH – 875,000 PRL
- 6606737 | 173 ETH – 865,000 PRL
5. ETH is withdrawn from KuCoin into 0x0001ee57bb28415742248d946d35c7f87cfd5a54:
- 6605411 | 65.9985593 ETH
- 6605489 | 61.6195307 ETH
- 6605692 | 24.1050992 ETH
Bruno also made a 100 ETH deposit into the Oyster Pearl Dual Sig contract in an attempt to misdirect attention towards the Oyster team: Link
Bruno’s motivations
Given this exploit always existed, why did Bruno elect to wait until that specific moment to pull the trigger? After all, it would’ve been twenty times more profitable for Bruno if he had executed this same plan during January 2018 when the price of PRL was over $4.
One line of reasoning is that the news of KuCoin’s impending policy of mandatory KYC for large withdrawals forced Bruno to take action. On November 1st, 2018, non-KYCed withdrawals would be limited to 2 BTC/ 24 hours and would severely restrict Bruno’s ability to monetize such an attack.
Another line of reasoning is that he had a falling out with the other members of the team and wanted to punish them now. This is the explanation that Bruno himself gave for why he did it:
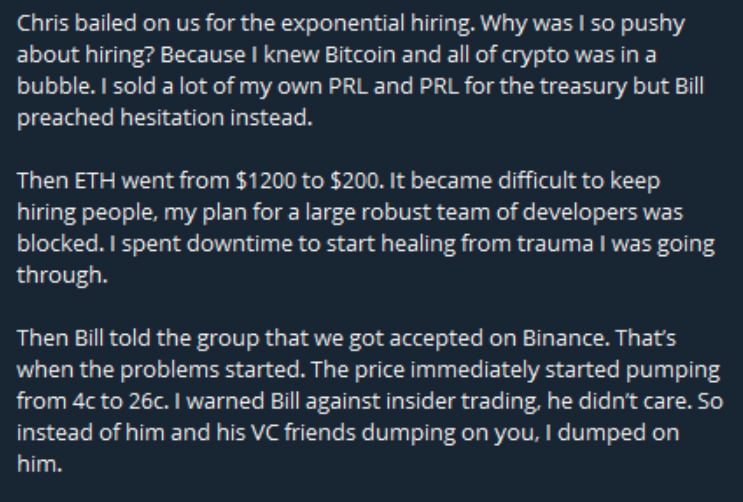
Source: Telegram group
Despite Oyster’s insistence that the smart contract passed multiple audits, including Quantstamp’s, they still left the contract’s directorship open for alleged technical reasons. This is what Bruno ultimately used to take over the ICO contract and siphon the tokens.
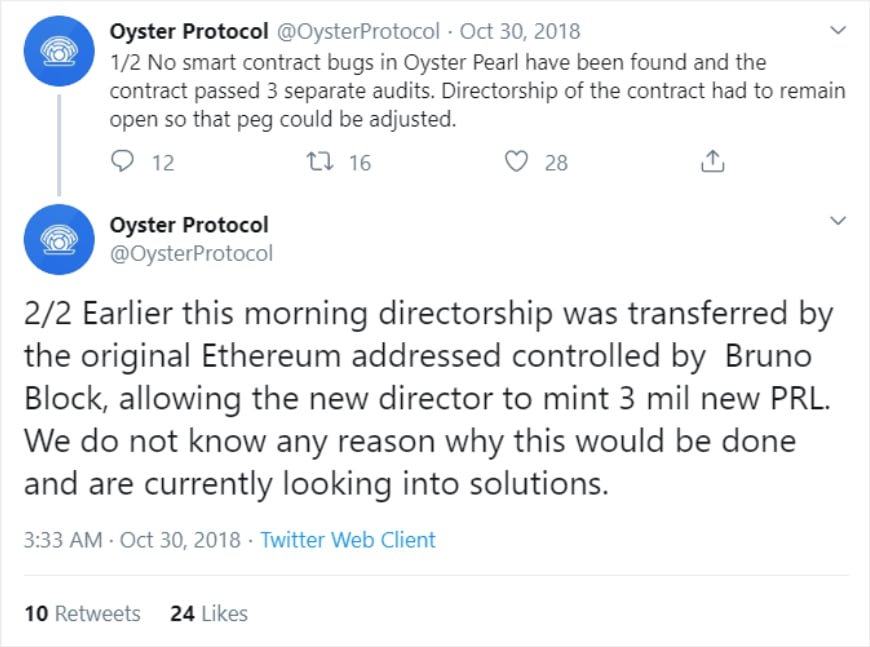
Source: Twitter
One may wonder how exactly the vulnerability passed three separate audits, or why the community was not more vigilant against this level of centralization. At the end of the day, trust was placed in the team and the team itself turned against one another.
So what happened to the project afterward? Amazingly, it still trots along on its mission. The Oyster team decided to fork to Opacity (OPQ), a coin which today is still listed on KuCoin with a US$2million market cap and a functioning cloud storage product. The Binance listing never came to fruition, and the damage done to the reputation of the project proved permanent and irreversible. Bruno Block, for his part, seemingly continues to work on his original vision for Oyster. He posts infrequent updates in Telegram with the last update coming on December 6th, 2019.
Takeaways
The story of Oyster Pearl should be understood as a warning to all cryptocurrency projects which have a centralized admin or director function accessible by specific individuals. Well-meaning people today may not be well-meaning people tomorrow, and ownership of keys controlling important contracts may even be sold without the knowledge of affected parties. Open source code is vulnerable when investors don’t read code, auditors are too conflicted to point out holes, and team members too dismissive of vulnerabilities from their own centralization.
Over the past year, the rapid growth in the DeFi space has come with a commensurate amount of accompanied hype. And yet, serious vulnerabilities in the largest DeFi projects have been uncovered as well:
- Compound: Ameen Soleimani notes that if the admin private key is compromised, all funds on the platform can, in fact, be drained.
- Maker: Micah Zoltu notes that someone holding 40,000 MKR can steal the entire ETH collateral in the system.
- Dydx: users point out that Dydx’s forced migration of users’ Single-Collateral Dai (SAI) to Multi-Collateral Dai (DAI) implies all funds are custodial, as they could presumably then convert users’ balances to a worthless token also if they so chose to.
What all three of these have in common is that they assume benevolent large actors who, via extra-protocol incentives, would not want to see the project fail. But then again, Bill must have thought that Bruno would never betray his own project, and he paid the price for his naivety. While teams will always brush off the dangers when things are going fine, the existence of such mechanisms means that these projects are always one stormy night away from financial devastation. The image of Taleb’s turkey springs to mind: a turkey getting fed and getting fatter day by day until one Thanksgiving Day it is slaughtered for a grand meal.
In the process of building trustless protocols, we should place intense scrutiny on where in fact trust is still being assumed. The fact that platforms are incentivized to hide these vulnerabilities while malicious actors are incentivized to exploit them when the conditions are right could mean that the risks are understated currently and may only be more apparent when the attack is over.
AUTHOR(S)
